
public key encryption
Learning Goal
I can explain how public key encryption functions to secure information sent over computer networks.
Introduction
When people (and computers) want to exchange data with each other securely on the internet, they use encryption. When typing passwords or credit card numbers into a website’s login screen, it's important that data safely makes it to the site’s servers.
Public key encryption is an asymmetric encryption technique which uses different keys for encryption and decryption, allowing computers to securely communicate with each other over the internet.
Let's try to simulate the process of public key encryption. Here are the steps in the simulation process.
1. Key Generation
Team A generates a public key and a private key (map) and publishes public key. Private key remains secret.
2. Key Exchange
Team A sends/publishes public key (map) and sends to Team B.
3. Encryption
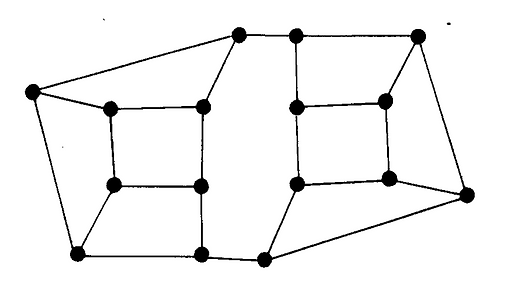
Team B chooses a number to send. Assigns values to each point on map that (when added) total desired number. Team B then encrypts message (number) by choosing any intersection, looking at it and its three neighbors-- four intersections in all-- and totals the numbers on them.Repeats for all other intersections on the map.

4. Sending Encrypted data
Team B then sends the map to Team A with only the parenthesized numbers on it.
5. Decryption
Team A uses the private map to decrypt the message by adding up only the secret marked intersections. Team A reveals the secret number.

How does it work?
The group of intersections in each partition (shown below) are exactly the ones summed to give the transmitted numbers for the marked intersections, so the sum of the four transmitted numbers on those intersections will be the sum of all the original numbers in the original map.

Try it!
Join a group of four, and split into two teams (Team A and Team B). With the public and private maps provided, follow the steps above.
When successful simulating the process with the maps provided, design your own map, keeping the private map secret and giving the public map to another team to encrypt. When they are done, use your private key to decrypt the message.